Gauntlet invites security researchers to responsibly disclose vulnerabilities in our Smart contracts, web applications, API and infrastructure. The program’s scope and details are listed below.
Aera: Gauntlet’s Vault Infrastructure
Gauntlet’s bug bounty program on Aera, our vault infrastructure, is provided via Immunefi.
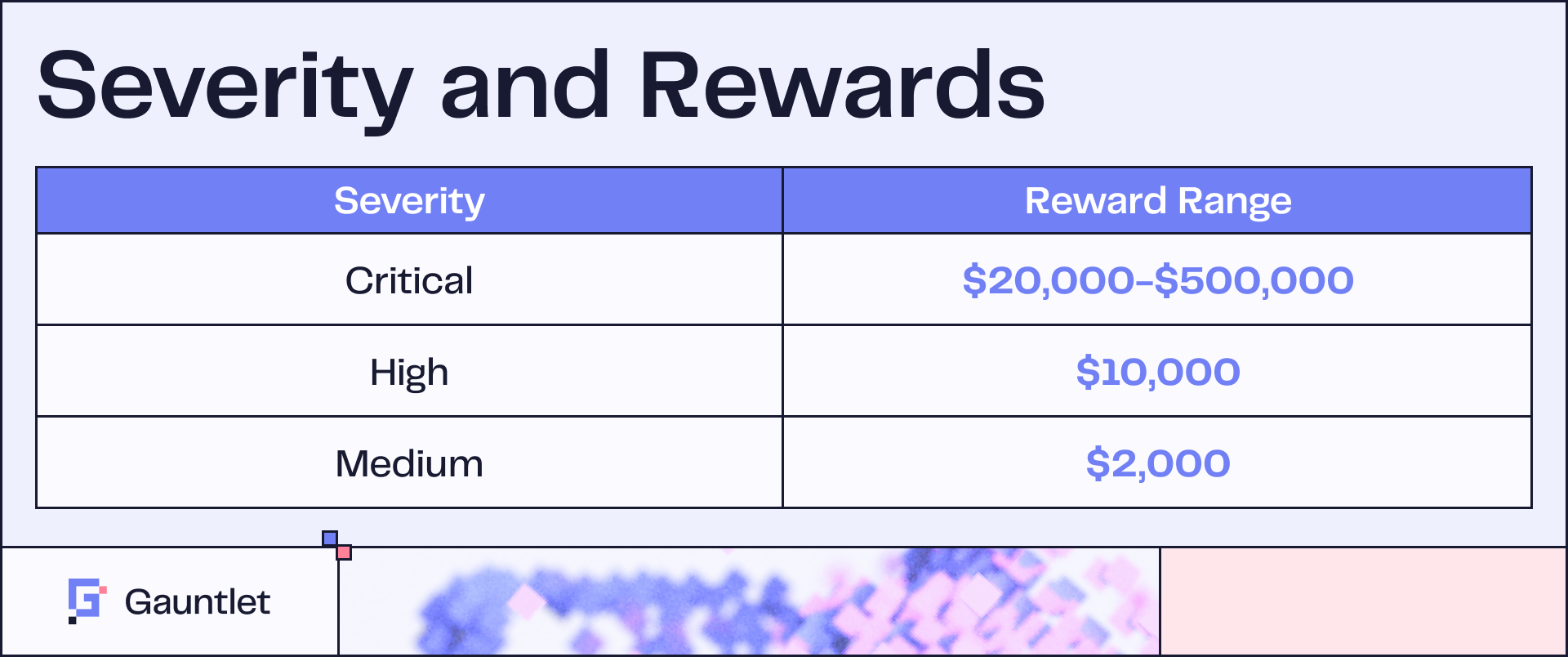
Rewards are distributed according to the impact the vulnerability could otherwise cause based on the Impacts in Scope. The final classification however takes into consideration the likelihood of the impact being achieved based on the table. When submitting a bug report, select the original assigned impact level, but please be aware that its severity level may be reassigned based on the likelihood according to this table. KYC is required. Rewards are paid out in USDC. Proof of concept is required for all severities.
In cases of repeatable attacks for smart contract bugs, only the first attack is considered if the smart contracts where the vulnerability exists can be upgraded, paused, or killed. If the attack impacts a smart contract directly holding funds that cannot be upgraded or paused, the amount of funds at risk will be calculated with the first attack being at 100% of the funds that could be stolen and then a reduction of 25% from the amount of the first attack for every 300 blocks the attack needs for subsequent attacks from the first attack, rounded down. For avoidance of doubt, if a second attack would happen at 600 blocks and then a third at 900 blocks, the funds at risk would be counted at 50% and 75% of the reward from the first attack, respectively.
Audits
- Spearbit — Report Link (9/21/2023)
- Spearbit — Report Link (5/6/2025)
- Spearbit — Report Link (6/24/2025)
Out of Scope
In addition to previously discovered bugs acknowledged in published audits or bug bounty competitions linked here, the following are out of scope:
- Risks of MEV in executed or submitted transactions
- Risks associated with an untrusted guardian, accountant or solver
- Risks associated with faulty oracles or third-party ERC20/ERC4626 asset implementations
- Risks associated with use of execute by treasury
- Risks associated with unsanctioned collusion of different roles (e.g., guardian and owner of asset registry)
Web Applications, API, and Infrastructure
Domains
- gauntlet.xyz (Primary domain & subdomains)
- aera.finance (Primary domain & subdomains)
REST APIs
- Aera Vaults API — Vault creation and ownership transfer across EVM chains (Base, Ethereum, Arbitrum, Optimism, Polygon). Endpoints under /v1/* and /v3/*.
- Metrics Store API — Unified metrics query API with CORS. Endpoints under /api/v1/* and /api/v2/*.
Out of Scope
- Third-party services not operated by Gauntlet.
- Social engineering, phishing or physical attacks.
- Denial of Service (DoS/DDoS) attacks.
- Automated scanning that degrades service availability.
- Vulnerabilities in dependencies where no exploit path exists in our usage.
- Internal-only services behind VPN or private subnets with no public exposure.
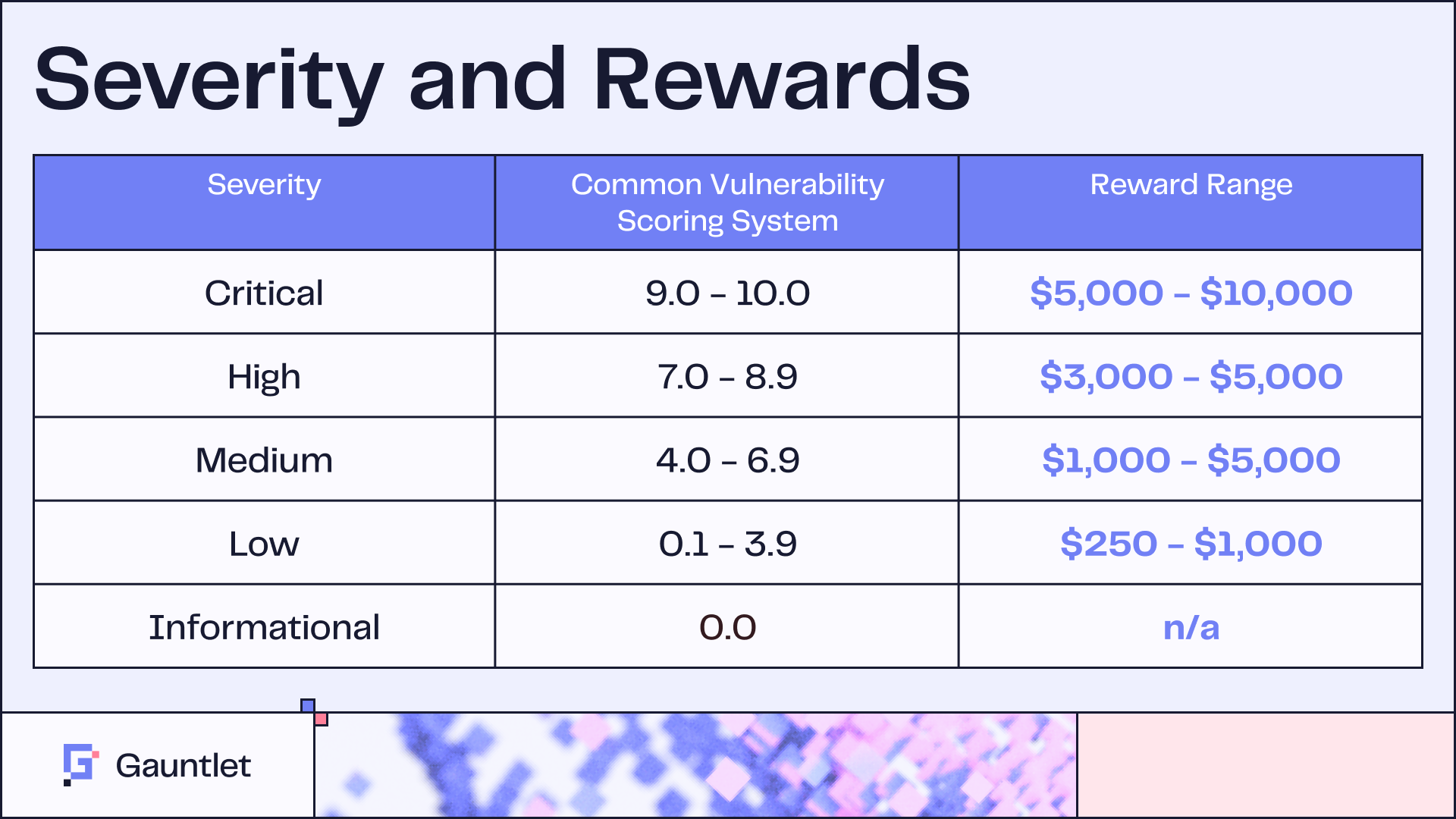
Reward amounts are determined at Gauntlet's discretion based on impact, exploitability, and report quality.
Vulnerability Categories of Interest
Critical
- Remote code execution (RCE) on any service
- Domain or subdomain hijacks
- Authentication/authorization bypass on protected services
- Unauthorized vault operations (creation, ownership transfer, fund movement)
High
- SSRF into internal-only services
- JWT verification bypass or token forgery
- Privilege escalation (read-only to admin)
- Secrets exposure (API keys, service account credentials)
Medium
- Insecure direct object references (IDOR)
- API query abuse leading to proprietary data leak
- SQL injections leading to proprietary data exfiltration or modification.
Rules of Engagement
- Do not perform denial-of-service attacks or any testing that degrades service availability.
- Do not modify, or delete data belonging to other users or vaults.
- Do not exfiltrate sensitive data beyond what is necessary to demonstrate the vulnerability.
- Do limit testing to the lowest level of access needed to confirm the vulnerability.
- Do stop testing and report immediately if you gain access to sensitive data or systems.
Reporting
How to Report
Send vulnerability reports to: [email protected]
Report Requirements
Each report must include:
- Summary — Brief description of the vulnerability
- Affected asset — Domain, endpoint, or service impacted
- Severity assessment — Your estimated CVSS score and justification
- Steps to reproduce — Clear, step-by-step reproduction instructions
- Proof of concept — Screenshots, HTTP requests/responses, scripts, or video
- Impact assessment — What an attacker could achieve with this vulnerability
- Suggested remediation — (Optional) Your recommended fix
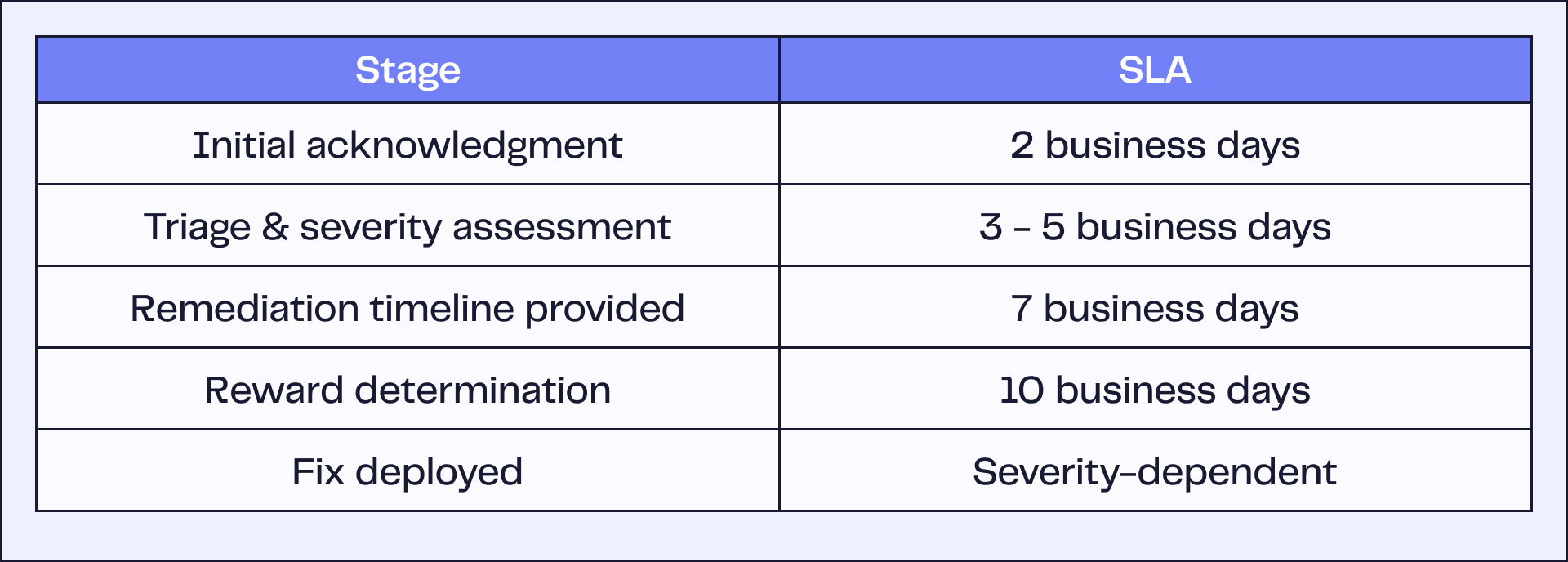
Response Timeline
Safe Harbor
Gauntlet will not pursue legal action against researchers who:
- Act in good faith and comply with this policy
- Report vulnerabilities promptly and do not publicly disclose before remediation
- Do not exploit vulnerabilities beyond what is necessary for demonstration
- Do not compromise user data, vault funds, or service availability
Exclusions
The following do not qualify for rewards:
- Findings from automated scanners without manual verification
- Missing best practices without demonstrable security impact
- Clickjacking on pages with no sensitive actions
- Self-XSS or issues requiring unlikely user interaction
- Software version disclosure without a known exploitable vulnerability
- SPF/DKIM/DMARC configuration issues
- Previously reported vulnerabilities (first report wins)
- Vulnerabilities requiring physical access
Disclosure Policy
- 90-day disclosure window — We request that researchers allow 90 days from report submission before public disclosure.
- We will coordinate with you on disclosure timing and credit.
- We are happy to credit researchers by name or handle in our security acknowledgments, unless anonymity is preferred.
Contact
- Security reports: [email protected]
- Program questions: [email protected]
- PGP key: Available upon request for encrypted submissions
Gauntlet reserves the right to modify this program at any time. Changes will be reflected in this document with an updated revision date.
Blog
View the full presentation
Read the full paper